Scale Measures to Meet Compliance and Governance
The modern digital workplace is a fluid concept, no longer tied to physical locations. Hence, nowadays the mobile workforce collaborates effectively through digital mediums and platforms such as Microsoft Teams. However, facilitating a seamless experience for widespread business operations is not enough; creating a resilient ecosystem that is secure is just as important. Therefore, IT departments need to scale security measures across networks and devices to ensure standards of compliance and governance are met.

Microsoft Teams security relies on both compliance practices and good governance so that issues such as unwieldy sprawl, and unauthorized or accidental sharing of data are monitored and prevented. That’s why it is necessary to ensure that Microsoft Teams is secure and protects data integrity.
Understanding Compliance and Governance for MS Teams Security
On one hand, compliance plans are focused on the limited goal of meeting the obligations of sets of regulations, making the approach towards dealing with them more tactical. On the other, governance is a long-haul game based on how a company can position its business controls in relation to ethics and risks while empowering its members to efficiently utilize platforms like Microsoft Teams. By these descriptions, Microsoft Teams’ governance and compliance may seem separate, but the risks they are designed to protect against are usually interdependent.
Securing Microsoft Teams with OOTB Governance and Compliance Features
For unobstructed collaboration, you need to ensure your Microsoft Teams environment is not suffering from sprawl, abandoned workspace, poor naming conventions, and poor search experience. At the same time, to ensure content protection across the Microsoft Teams ecosystem, an organization must establish an information protection architecture so that your data stays trackable, protected, and compliant.
Let us help you tighten the security loopholes and meet the governance and compliance requirements with existing MS Teams functionalities:
1. Control Creation of Teams
Among the most important governance considerations for Microsoft Teams is controlling the creation of teams in the platform. By controlling who can request teams and create groups in Microsoft 365, you can prevent duplication of similar or overlapping workspaces, maintain a standardized user experience across the platform, and cut down on sprawl.
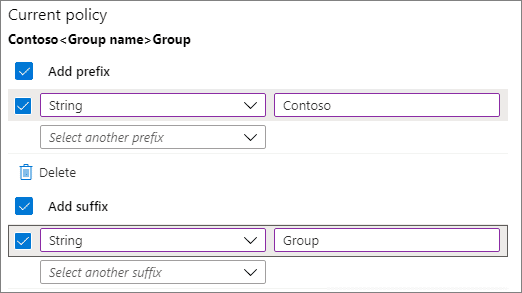
2. Naming Conventions
The ability to add a naming convention is crucial to eliminating confusion and minimizing sprawl in the environment. How you name your teams impacts the findability and usage of the overall MS Teams ecosystem. You should configure a group naming policy to add a specific prefix/suffix to the group name, as well as set a list of blocked words that you don’t want to be included in the names of teams and channels.
3. Application Management
End users have the option to customize their Microsoft Teams experience by adding third-party apps to it. However, from a governance and compliance perspective, this can pose some serious challenges for IT departments, as they need to ensure no confidential data is being leaked to unvetted sources. You need to configure which apps to give access to and which apps will act as the default for your users.
4. Data Retention Policies
You can create retention policies to specify when to store Microsoft Teams data to stay compliant with business, regulatory or litigation requirements and manage the removal of data that is no longer needed. Apply retention policies to your entire organization, specific teams, or users to store the data for a specified period before deletion or to be stored elsewhere.
5. Advanced Threat Protection (ATP)
With Advanced Threat Protection, you can detect and block user access to malicious content in Microsoft Teams. It helps ward off unsafe files in file-sharing platforms integrated with MS Teams, like SharePoint and OneDrive.
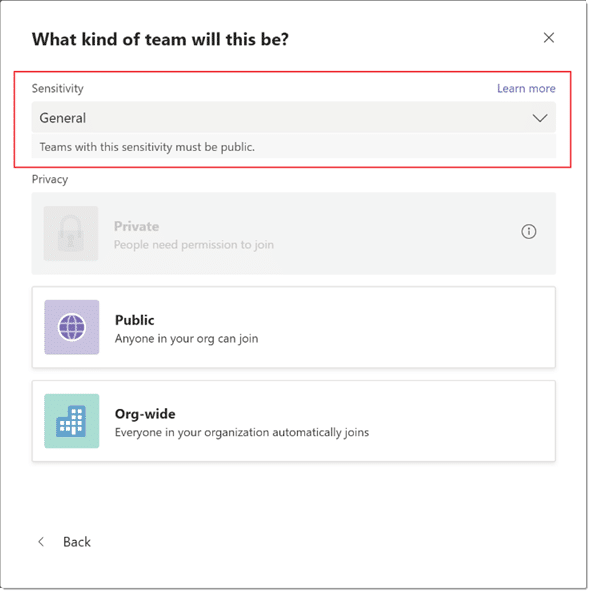
6. Sensitivity Labels
The built-in Microsoft Information Protection (MIP) sensitivity labels enable the classification and protection of your Microsoft Teams data. Enable the creation and definition of sensitivity labels as a requirement to ensure all your “secret” data is encrypted. These labels help you, control external sharing, configure the privacy of teams, and manage access from unmanaged devices.
7. Data Loss Prevention (DLP)
Set up DLP policies to automatically block unauthorized users from accessing or sharing sensitive data in messages (i.e., private chats, channels, shared channels), or documentation. With DLP you enforce secure user behavior in MS Teams and prevent data breaches. Quick Tip: Accurately classifying and labeling the data shared in Microsoft Teams ensures your DLP policy actions are applied correctly.
8. Electronic Discovery (eDiscovery) and Legal Hold
eDiscovery recreates conversations that took place within Microsoft Teams for the legal team to get the entire context of the conversations to be used as evidence in legal cases. In addition, you assign members with specialized permissions to an eDiscovery case and define the parameters of a search query for content relevant to an investigation.
Partner with Klarinet Solutions for a Secure Microsoft Teams Implementation
Choosing your partner for Microsoft Teams security right from the start of the deployment journey is critical to adoption success. Therefore, you need a solution provider that prioritizes the platform’s adoption, governance, and engagement from day one of the rollout.
Lean on the expertise and knowledge of Klarinet Solutions to pre-plan the setup and usage of Microsoft Teams in your organization. An experienced player in the industry, Klarinet Solutions will ensure a rapid rollout with effective Microsoft Teams security. Engage with the team to transition from Microsoft Teams chaos to control with compliance.